Bypass 40X Response Codes with dontgo403
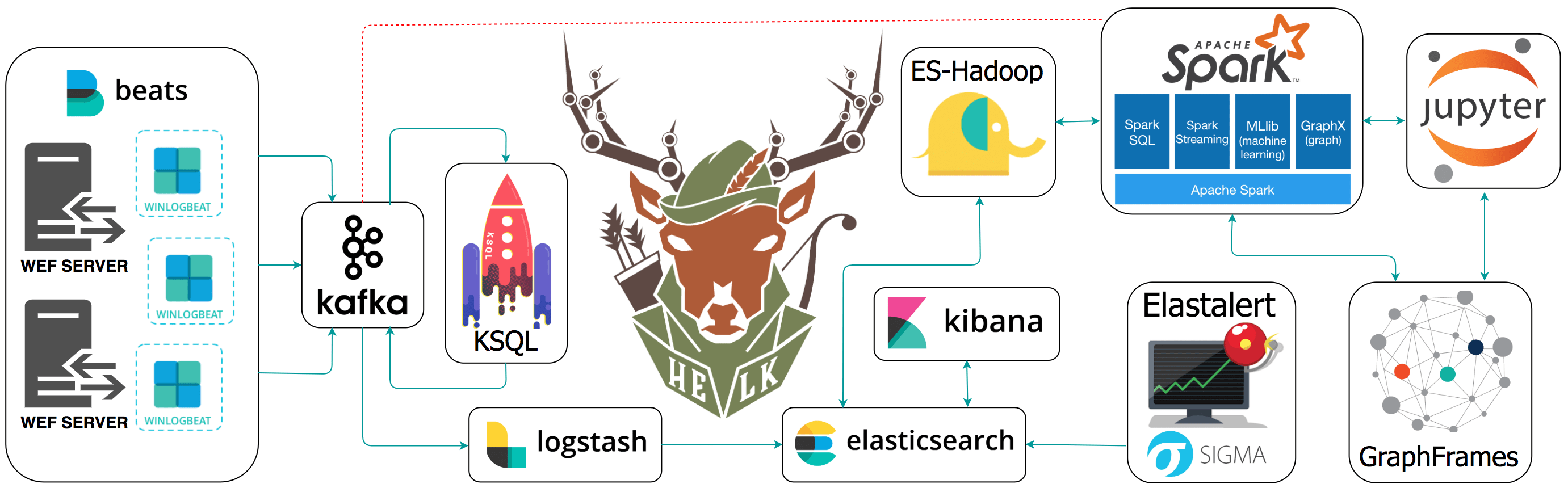
Read More »HELK – An Open Source Threat Hunting Platform
The Hunting ELK or simply the HELK is an Open Source Threat Hunting Platform with advanced analytics capabilities such as SQL declarative language, graphing, structured streaming, and even machine learning via Jupyter notebooks and Apache Spark over an ELK stack.
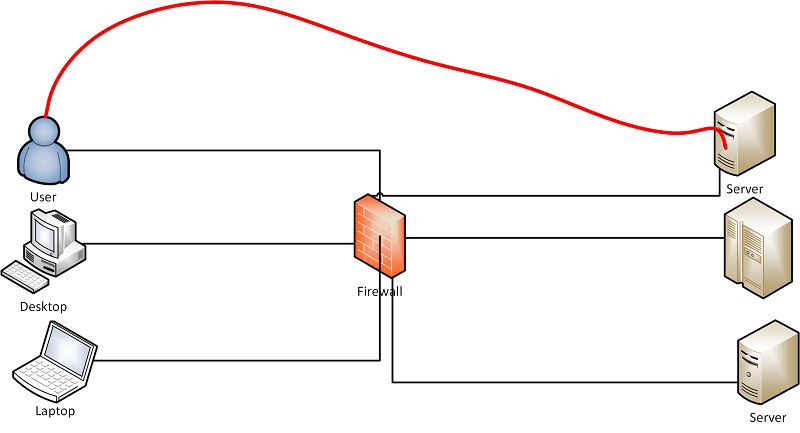
Read More »Use any Linux applications through a proxy (apt-get, wget etc)
It's pretty normal in many Organizations to use get servers to connect to Internet via a Proxy. In most cases it's for updating apt-get or yum via proxy. However, quite often you might need to download packages directly using wget or curl and setting up apt-get or apt via proxy, wget via proxy, curl via proxy is a pain. What if you could simply setup a Proxy and just use any applications to use that using a simply command? I faced this many times and hence writing this guide. Note that if you're only allowing apt-get via proxy then stick with configuring /etc/apt.conf or /etc/apt/conf.d/00proxy or something similar but if you need to allow different applications via a proxy then this method is best and simplest.
Read More »Targeting websites with Password Reset Poisoning
Most of web application security vulnerabilities, leverage user input in ways that were not initially intended by their developer(s). Password Reset Poisoning is one such vulnerability, that leverages commonly unthought of headers, such as the Host header seen in an HTTP request: GET https://example.com/[email protected] HTTP/1.1 Host: evilhost.com Notice the difference …
Read More »Identify website technologies with WhatWeb
WhatWeb Identify website technologies including content management systems (CMS), blogging platforms, statistic/analytics packages, JavaScript libraries, web servers, and embedded devices.
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….