Recommended best practices for mitigating this threat include rigorous credential and privileged-access management, as well as remote-access control, and audits of legitimate remote-access logs. While these measures aim to prevent the initial attack vectors and the spread of malicious activity, there is no single proven threat response. Using a defense-in-depth …
Read More »Advanced Persistent Threat Activity Exploiting Managed Service Providers
Organizations should configure system logs to detect incidents and to identify the type and scope of malicious activity. Properly configured logs enable rapid containment and appropriate response. Response An organization’s ability to rapidly respond to and recover from an incident begins with the development of an incident response capability. An …
Read More »Publicly Available Tools Seen in Cyber Incidents Worldwide
Remote Access Trojan: JBiFrost First observed in May 2015, the JBiFrost RAT is a variant of the Adwind RAT, with roots stretching back to the Frutas RAT from 2012. A RAT is a program that, once installed on a victim’s machine, allows remote administrative control. In a malicious context, it …
Read More »Catching bad guys
Ever wondered how the good guys catch bad guys? I meant to say, what’s the process of catching bad guys who create virus, malware, crypto-lockers? It’s sort of a grey area and mostly not discussed very openly about the different methodologies used for Catching bad guys who create and distribute …
Read More »dns2proxy – Offensive DNS server post-explotation tool – DNS spoofing, phishing and pharming
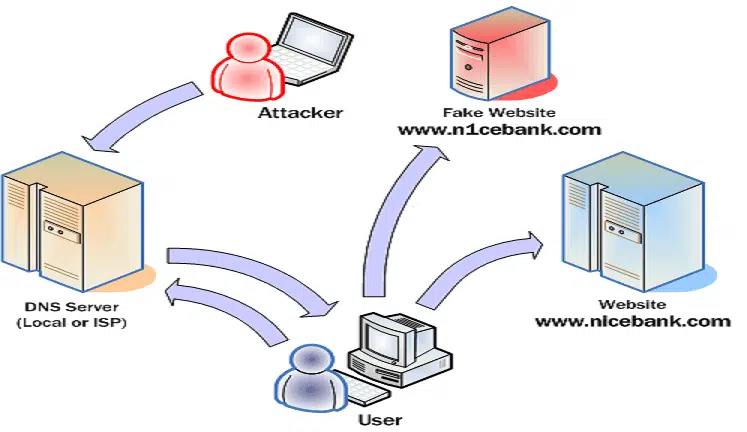
dns2proxy is an offensive DNS server that offers various features for post-exploitation once you’ve changed the DNS server of a victim. This tools offers different features for post-explotation once you change the DNS server of a Victim. DNS spoofing, also referred to as DNS cache poisoning, is a form of …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….