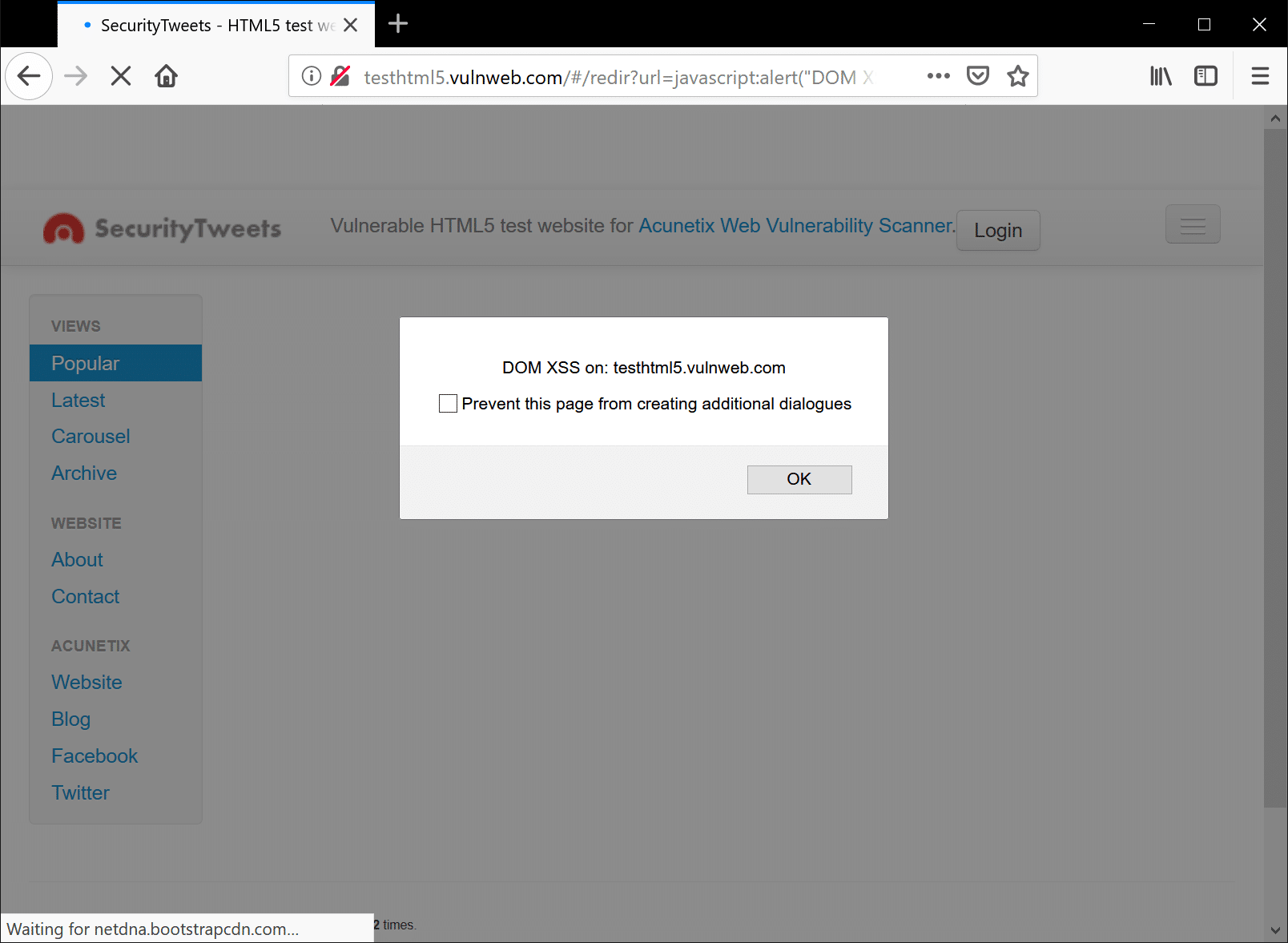
There’s no denying the role that JavaScript has played in making web applications the sleek, interactive, online experiences that we know and love today. This powerful scripting language brought interactivity and animation to the web. But with great power comes great responsibility. Cross-site-scripting (XSS) remains a persistent stalwart among the …
Read More »Inception Attackers Target Europe with Year-old Office Vulnerability
The Inception attackers have been active since at least 2014 and have been documented previously by both Blue Coat and Symantec; historical attacks used custom malware for a variety of platforms, and targeting a range of industries, primarily in Russia, but also around the world. This blog describes attacks against …
Read More »Targeting websites with Password Reset Poisoning
Most of web application security vulnerabilities, leverage user input in ways that were not initially intended by their developer(s). Password Reset Poisoning is one such vulnerability, that leverages commonly unthought of headers, such as the Host header seen in an HTTP request: GET https://example.com/[email protected] HTTP/1.1 Host: evilhost.com Notice the difference …
Read More »Check Point SandBlast protected users from a Zero-Day Microsoft Office Vulnerability
Neil Armstrong, the great space explorer, once said “research is all about creating new knowledge.” And of course, with knowledge we are in a better position to predict, and thus prepare, for what is yet to come. For this reason, the work Check Point Research does is invaluable when it …
Read More »What are the Challenges of Using Open Source Cybersecurity Tools?
By making their source code freely available, developers of open source software rely on the power of the wider community in order to help them audit and improve their code. Not only this but also by involving the wider community of users in the development of software, a broader spectrum …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….