In the never-ending arms race between threat actors and defenders, automation and machine learning have become your ultimate weapons. Today, threat actors employ automation in countless ways to speed up their attacks and evade detection. Outpacing attackers requires the effective use of automation and machine learning. Years ago, our research …
Read More »Information gathering and correlation with Unicornscan on Kali Linux
Unicornscan is a new information gathering and correlation engine built for and by members of the security research and testing communities. It was designed to provide an engine that is Scalable, Accurate, Flexible, and Efficient. It is released for the community to use under the terms of the GPL license. …
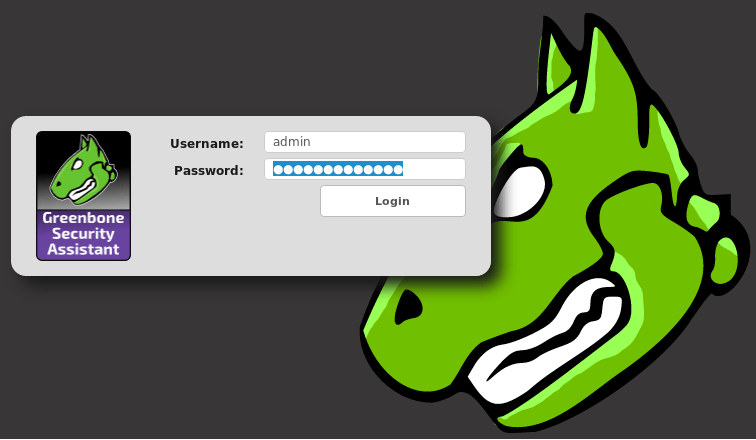
Read More »Configure, Tune, Run and Automate OpenVAS on Kali Linux
Users often request the addition of vulnerability scanners to Kali, most notably the ones that begin with “N”, but due to licensing constraints, we do not include them in the distribution. Fortunately, Kali includes the very capable OpenVAS, which is free and open source. Although we briefly covered OpenVAS in …
Read More »Install, setup, configure and run OpenVAS on Kali Linux
Vulnerability scanning is a crucial phase of a penetration test and having an updated vulnerability scanner in your security toolkit can often make a real difference by helping you discover overlooked vulnerable items. For this reason, we’ve manually packaged the latest and newly released OpenVAS 8.0 tool and libraries for …
Read More »Blue Coat ProxySG and ASG Appliances – cannot delete a host now in use by policy
Symantec ProxySG and Advanced Secure Gateway (ASG) which was previously listed as Blue Coat Systems, acquired by Symantec in 2016. Symantec ProxySG and Advanced Secure Gateway (ASG) are high performance on-premises appliances that protect organizations across the web, social media, applications and mobile networks. Combine with cloud-delivered Web Security Service …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….