Encrypted internet traffic is on an explosive upturn. According to the Google® Transparency Report: “Users load more than half of the pages they view over HTTPS and spend two-thirds of their time on HTTPS pages.”[1] At the same time, encrypted traffic carried nearly 3.5 million unique malware samples in 2017. …
Read More »Setting Up A Free TLS/SSL Certificate With “Let’s Encrypt”
SSL (Secure Sockets Layer) is the standard security technology for establishing an encrypted link between a web server and a browser. This link ensures that all data passed between the web server and browsers remain private and integral. SSL is an industry standard and is used by millions of websites …
Read More »Catching bad guys
Ever wondered how the good guys catch bad guys? I meant to say, what’s the process of catching bad guys who create virus, malware, crypto-lockers? It’s sort of a grey area and mostly not discussed very openly about the different methodologies used for Catching bad guys who create and distribute …
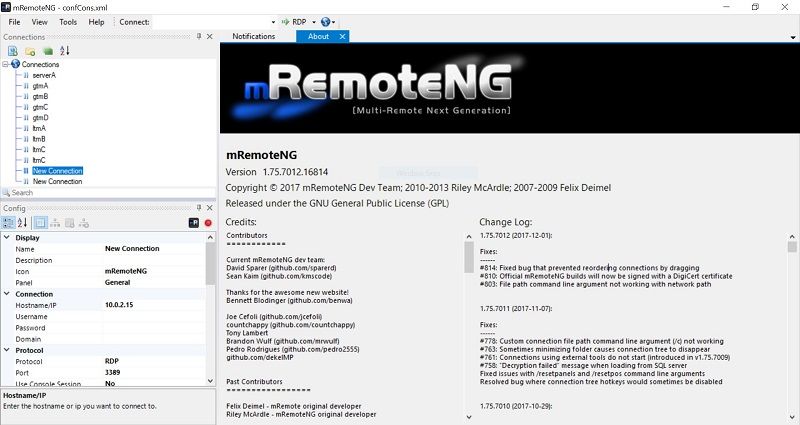
Read More »PuTTY alternatives
PuTTY is the most popular SSH client for Windows based systems. In fact it’s so popular that people actually install it in Linux (apt-get install putty)I. PuTTY is easy to use and you can save a lot of preferences. However, is PuTTY is best? To be honest, I think not. …
Read More »Wireless WPA2 password cracking using KRACK attacks
We discovered serious weaknesses in WPA2, a protocol that secures all modern protected Wi-Fi networks. An attacker within range of a victim can exploit these weaknesses using key reinstallation attacks (KRACKs). Concretely, attackers can use this novel attack technique to read information that was previously assumed to be safely encrypted. …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….