This Kali release is the first to include the Linux 4.15 kernel, which includes the x86 and x64 fixes for the much-hyped Spectre and Meltdown vulnerabilities. It also includes much better support for AMD GPUs and support for AMD Secure Encrypted Virtualization, which allows for encrypting virtual machine memory such …
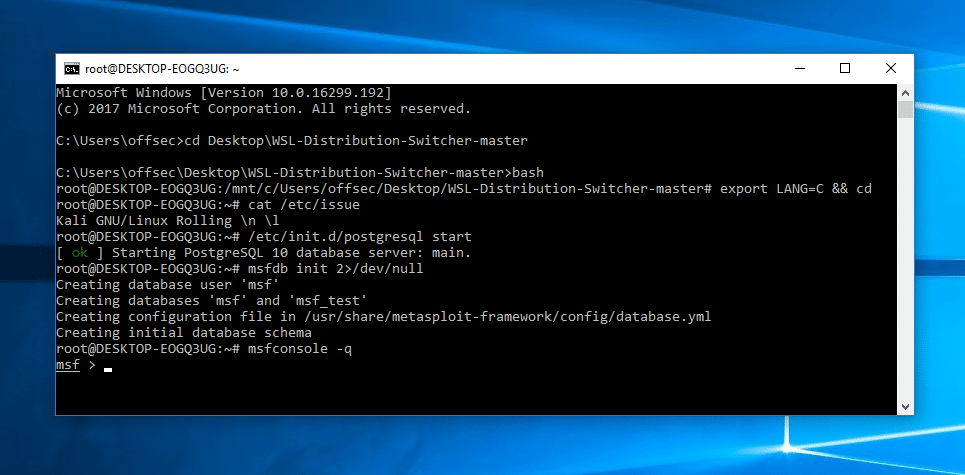
Read More »Kali Linux on Windows Subsystem for Linux
Kali Linux developers and Offensive Security team is always trying to find new ideas and better ways to run Kali Linux. With the recent introduction of Windows Subsystem for Linux (WSL) in Windows 10, it opened a new way to run Kali Linux. Tell me, do you play games? Sure. …
Read More »Find Linux Exploits by Kernel version
Sometimes it’s really hard to find the correct exploit for the device that you are pentesting. I found two good references that may be helpful or least will give you a good starting point. Both of these resources can suggest Linux exploits based on kernel version. The first one is …
Read More »Kali Linux Cheat Sheet for Penetration Testers
Penetration testing (also called pen testing) is the practice of testing a computer system, network or Web application to find vulnerabilities that an attacker could exploit. Kali Linux Cheat Sheet for Penetration testers is a high level overview for typical penetration testing environment ranging from nmap, sqlmap, ipv4, enumeration, fingerprinting …
Read More »How to search exploits in metasploit?
Metasploit was created by H. D. Moore in 2003 as a portable network tool using Perl. By 2007, the Metasploit Framework had been completely rewritten in Ruby. On October 21, 2009, the Metasploit Project announced that it had been acquired by Rapid7, a security company that provides unified vulnerability management …
Read More » blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….