Did you knew every time you fill in your username …
Read More »
March 5, 2024
Whispers: A Powerful Static Code Analysis Tool for Credential Detection
“My little birds are everywhere, even in the North, they whisper to me the strangest stories.&…
March 5, 2024
Enabling AMD GPU for Hashcat on Kali Linux: A Quick Guide
If you’ve encountered an issue where Hashcat initially only recognizes your CPU and not the GP…
March 5, 2024
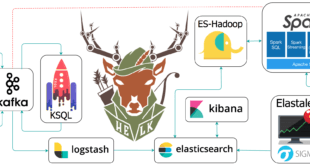
Identifying harmful activity on your captured traffic
This Python script utilises Wireshark or TCPdump to analyse network traffic stored in a specified .p…
May 20, 2023
Nyxt: Hacker’s Dream Browser
In the ever-evolving digital landscape, the demand for specialized tools and platforms has grown exp…
May 19, 2023
Migrate Plex Server – Ubuntu
To migrate your Plex server to a new Ubuntu server, you can follow these steps: 1. Set up the new Ub…
May 19, 2023
Boot Ubuntu Server 22.04 LTS from USB SSD on Raspberry Pi 4
This is a guide for configuring Raspberry Pi4 to boot Ubuntu from external USB SSD drive instead of …
April 26, 2023
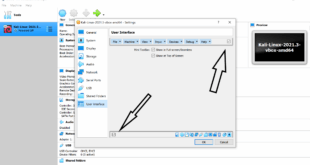
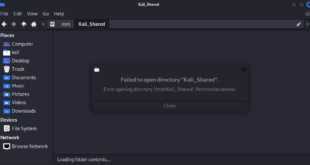
How to fix You can’t access this shared folder because your organization’s security policies block unauthenticated guest access error on Windows 11
If you have the following error on Windows 11 “You can’t access this shared folder becau…
June 11, 2022
Ubiquiti Dream Machine (UDM) – unable to connect to NBN
I don’t want the NBN ISP router running anymore and use Ubiquiti Dream Machine (UDM) instead. …
April 15, 2022
Quick Snap Cheat Sheet for Ubuntu
Snaps are app packages for desktop, cloud and IoT that are easy to install, secure, cross‐platform a…
February 11, 2022
Bypass 40X Response Codes with dontgo403
Bypass 40X Response Codes with dontgo403 …
Recent Posts
-
Advantages disadvantages of using Proxy vs VPN vs TOR vs TOR and VPN together.
What makes you truly anonymous and leaves next to no …
Read More » -
Complete solution for online privacy with own private OpenSSH, OpenVPN and VNC server
-
Free VPN providers of 2015
-
A very detailed guide on how to setup VPN on Kali Linux and Ubuntu
-
Cracking Wifi WPA/WPA2 passwords using pyrit cowpatty in Kali Linux
Cracking Wifi WPA/WPA2 passwords using pyrit cowpatty– with cuda or …
Read More » -
Fixing dpkg: warning: ‘ldconfig’ not found in PATH or not executable error when installing packages.
-
Kali Linux on Windows Subsystem for Linux
-
Configure, Tune, Run and Automate OpenVAS on Kali Linux
-
TP-Link TL-WDN3200 N600 Wireless Dual Band USB Adapter in Linux
I’ve got this TP-Link TL-WDN3200 N600 Wireless Dual Band USB …
Read More » -
Poll: Vote for best USB Wireless cards for Kali Linux
-
Cracking WPA2 WPA with Hashcat in Kali Linux (BruteForce MASK based attack on Wifi passwords)
-
Wireless WPA2 password cracking using KRACK attacks
-
Generating self-signed x509 certificate with 2048-bit key and sign with sha256 hash using OpenSSL
With Google, Microsoft and every major technological giants sunsetting sha-1 …
Read More » -
Whispers: A Powerful Static Code Analysis Tool for Credential Detection
-
How to search exploits in metasploit?
-
US Govt wants you to hack the Pentagon and get rewarded for it
-
Output your microphone to a remote computers speaker
Output your microphone to a remote computers speaker
Read More » -
SSH through host in the middle
-
Three different ways to duplicate installed packages in multiple machines in Linux
-
ssh to machine behind shared NAT
-
How to check Network Interface details in Linux
 blackMORE Ops Learn one trick a day ….
blackMORE Ops Learn one trick a day ….